Picture a machine so powerful it could crack open your bank account’s security the way you’d crack open an egg. No tools, no brute force, just pure computational elegance. That’s the promise at the heart of quantum computing, a technology once confined to the blackboards of theoretical physicists that is now drawing in billions of dollars, government mandates, and some very nervous cybersecurity professionals. The idea of a quantum computer sitting in your living room still sounds like science fiction, and honestly, for now, it is. But the gap between fiction and reality is closing faster than most people realize. So let’s dive in.
The Machine That Thinks in Superposition
To understand why quantum computers are such a big deal, you first need to understand how different they are from anything we’ve built before. Your laptop uses bits that are either 0 or 1. Quantum systems use qubits that can be 0, 1, or both simultaneously through superposition. The power jump is exponential, not linear. Think of it like this: a regular computer walks through a maze one corridor at a time. A quantum computer explores every corridor at once.
A set of just 2 qubits can simultaneously represent four values. With 3 qubits you get eight values, and it keeps doubling. Quantum computers can explore many solution paths at once instead of marching through them one by one. Then there’s entanglement, the deeply strange quantum property where measuring one qubit instantly tells you something about another, no matter how far apart they are.
Quantum computing poses serious risks to current cryptographic systems, especially public-key algorithms like RSA and ECC, which are vulnerable to Shor’s algorithm. Similarly, Grover’s algorithm threatens symmetric encryption by halving effective key lengths, demanding larger keys and more resources. These aren’t theoretical concerns. They are the reasons governments and tech giants are already in panic-planning mode.
IBM’s 1,121-Qubit Condor: The Milestone That Changed the Conversation
IBM Condor is a 1,121-qubit quantum processor created by IBM, unveiled during the IBM Quantum Summit 2023, which occurred on December 4, 2023. It was a landmark moment in the so-called “qubit arms race,” and it sent a clear signal that the industry had moved well past proof-of-concept.
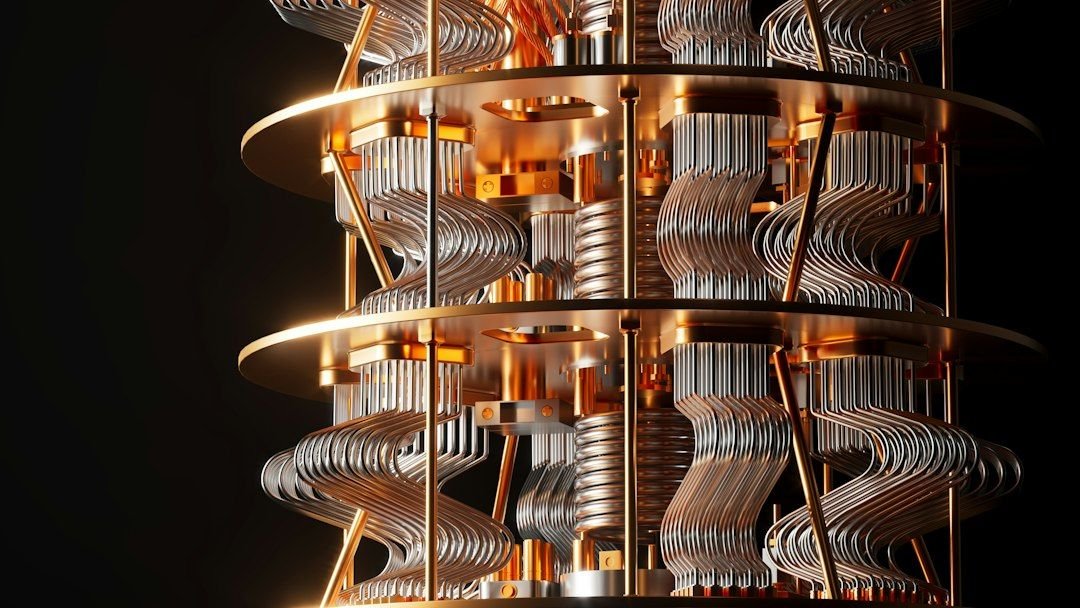
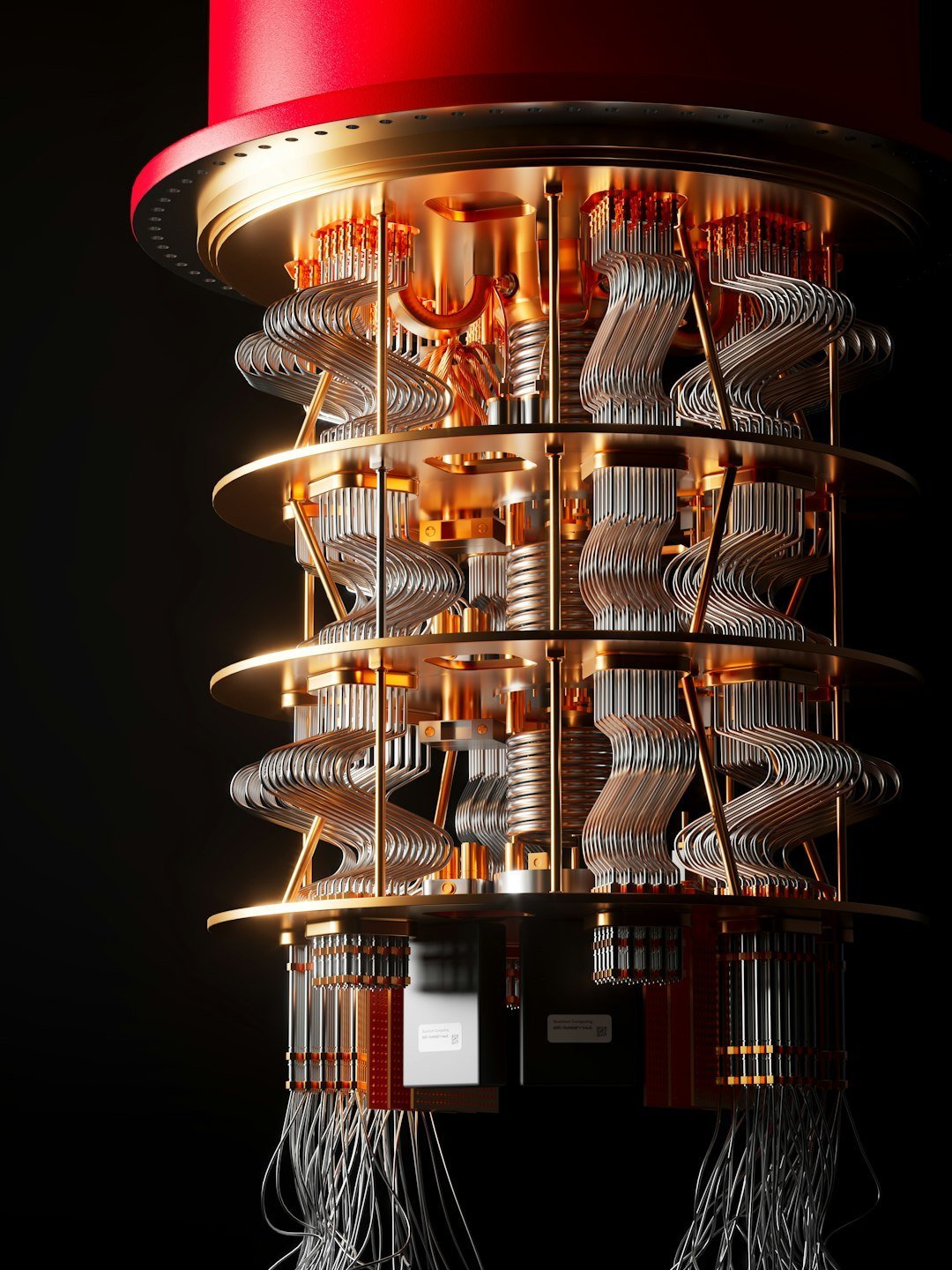
IBM introduced Condor, a 1,121 superconducting qubit quantum processor based on its cross-resonance gate technology. Condor pushes the limits of scale and yield in chip design with a 50% increase in qubit density and includes over a mile of high-density cryogenic flex IO wiring within a single dilution refrigerator. With performance comparable to IBM’s previous 433-qubit Osprey, it serves as an innovation milestone, solving scale and informing future hardware design.
Despite its impressive scale, the Condor processor is not a fault-tolerant machine. Its qubits are noisy intermediate-scale quantum qubits, meaning they are still prone to errors and have limited coherence times. Running a complex algorithm on Condor without sophisticated error mitigation would likely yield unreliable results. So yes, incredible progress. But also, still a long way from cracking the internet’s locks.
Why “Quantum at Home” Is Still a Fantasy (For Now)

Here’s the thing people keep getting wrong when they imagine some teenager running a quantum computer in their bedroom: the engineering involved is staggering. The Condor processor is packaged in a refrigerator that operates at a temperature colder than outer space to maintain the qubits’ fragile quantum states. That’s not a metaphor. It literally runs colder than the void between galaxies.
IBM’s Goldeneye cooling system can cool an area of over 1 cubic meter to near absolute zero. It maintains temperatures in the millikelvin range, close to absolute zero, necessary for the stability and functionality of superconducting qubits. You’re not fitting that in an apartment, and you’re definitely not powering it with a standard electrical outlet.
The hardware requirements alone make home use impossible in the near term. Qubits quickly forget their quantum states due to interaction with the outside world. The biggest challenge is figuring out how to control large systems of these qubits for long enough, and with few enough errors, to run the complex quantum circuits required by future quantum applications. It’s a bit like trying to balance a thousand spinning tops simultaneously in a room with even the slightest vibration. One wrong move and the whole calculation collapses.
The Encryption Crisis: Real, But Not Here Yet

I know it sounds scary, and it should raise some eyebrows, but let’s be precise about the timeline. Survey respondents believe the quantum threat is “looming,” with a cryptographically relevant quantum computer quite possible within the next 10 years, and likely in the next 15. That’s not imminent doom, but it’s also not comfortably distant.
Recent months have delivered a cluster of results, from Gidney’s sub-million-qubit RSA factoring estimates to Google Quantum AI’s ECC resource reductions to demonstrations of error correction beyond break-even on multiple hardware platforms, that have materially shifted the field’s assumptions about how much hardware a cryptographically relevant quantum computer actually requires. Translation: the goalposts just moved closer.
Recent analyses underscore the urgency of quantum threats. According to the Global Risk Institute’s 2024 Quantum Threat Timeline Report, experts estimate that within 5 to 15 years, a cryptographically relevant quantum computer could break standard encryptions in under 24 hours. That figure is the one that keeps cybersecurity professionals up at night, and rightfully so.
Harvest Now, Decrypt Later: The Threat Already in Motion

Here’s where things get genuinely chilling. The risk from quantum computing isn’t just about what happens when the machines arrive. The danger has already started. The quantum threat isn’t just about the future. Data encrypted today is already at risk. Nation-state adversaries and other bad actors are stealing sensitive information now, with the intent to decrypt it later using quantum tools once available. This tactic, known as “harvest now, decrypt later” attacks, targets data with long-term sensitivity.
This concern is embodied in the harvest now, decrypt later paradigm, in which encrypted communications captured today could be retrospectively decrypted once quantum capabilities mature. This scenario is especially troubling for data with long-term confidentiality requirements, such as classified government documents, healthcare records, or corporate trade secrets.
Google says it is setting a timeline to migrate to post-quantum cryptography by 2029, warning that action is needed before “a future quantum computer can break current encryption.” That’s a major company essentially admitting this isn’t a theoretical worry anymore. It’s a countdown.
NIST’s Post-Quantum Standards: The Defense Is Already Being Built

The good news is that the world hasn’t been sitting still. The U.S. Department of Commerce’s National Institute of Standards and Technology has finalized its principal set of encryption algorithms designed to withstand cyberattacks from a quantum computer. Researchers around the world are racing to build quantum computers that could break the current encryption that provides security and privacy for just about everything we do online.
In August 2024, NIST finalized three post-quantum cryptography standards: FIPS 203, FIPS 204, and FIPS 205. In March 2025, HQC was selected as an additional key encapsulation mechanism. These standards provide the algorithmic foundation for quantum-safe cryptography migration worldwide. The algorithms underlying these standards, including CRYSTALS-Kyber and CRYSTALS-Dilithium, are designed to withstand attacks from quantum machines that don’t even exist yet.
The standards are the result of an eight-year effort managed by NIST, which has a long history of developing encryption, and the agency rallied the world’s cryptography experts to conceive, submit, and then evaluate cryptographic algorithms that could resist the assault of quantum computers. Eight years. That’s how seriously the global security community has been taking this, even when most headlines were focused elsewhere.
Governments Are Racing and the Money Is Flowing

Governments around the world have woken up fast. Governments are increasingly urging companies to begin preparing for the shift, recognizing that the transition will take time. Countries including the United Kingdom, France, Germany, the Netherlands, and the United States have all published strategies, guidelines, or white papers outlining the risks and the need for action.
The European Commission’s Coordinated PQC Transition Roadmap mandates deployment of post-quantum encryption across all EU member states beginning in 2026, with critical infrastructure operators completing their transition by end of 2030. That is not a suggestion. That is a legal mandate, and it starts this year.
The investment figures are equally striking. In 2024, investors poured nearly $2.0 billion into quantum technology startups worldwide, a 50 percent increase compared to $1.3 billion in 2023. Public funding hit $10 billion by April 2025, spiked by investment announcements of $7.4 billion from Japan and $900 million from Spain. Other national announcements include Australia’s $620 million commitment to creating the world’s first utility-scale, fault-tolerant quantum computer. The numbers tell the story: this is now a global arms race.
The Economic Stakes: Trillions on the Table

Let’s zoom out for a moment and look at what’s really at stake economically. McKinsey’s analysis shows that the four industries likely to see the earliest economic impact from quantum computing, including automotive, chemicals, financial services, and life sciences, stand to potentially gain up to $1.3 trillion in value by 2035. That’s not pocket change. That’s a fundamental reshaping of entire industries.
McKinsey’s research shows that the three core pillars of quantum technology could together generate up to $97 billion in revenue worldwide by 2035. Quantum computing will capture the bulk of that revenue, growing from $4 billion in revenue in 2024 to as much as $72 billion in 2035. While quantum technology will affect many industries, the chemicals, life sciences, finance, and mobility industries will see the most growth.
Industry research has already warned that quantum computing could make even the most secure financial systems vulnerable. Banks, payment networks, and digital exchanges are not waiting around to find out. Organizations should develop cryptographic agility, the ability to add or swap cryptographic systems quickly and cleanly. That capability pays off beyond quantum threats, preparing teams for new math, fresh attack techniques, or surprises no one has named yet. It’s the kind of strategic thinking that separates the prepared from the panicked.
Conclusion: A Race Between Two Clocks

Here’s the honest takeaway from everything we know in 2026: quantum computing is not going to make encryption obsolete tomorrow. The hardware is still too large, too cold, too fragile, and too error-prone to live in your home or to crack military-grade encryption today. Breakthroughs in quantum technology, including quantum error correction, have led to a predicted arrival date of 2030 for fault-tolerant quantum computing, with increasing indications by companies for an even earlier arrival.
The real story isn’t about some sudden overnight collapse of cybersecurity. It’s a slow-motion race between two clocks: one counting down to a quantum computer powerful enough to break today’s encryption, and another counting toward the global adoption of quantum-safe standards. The “harvest now, decrypt later” threat means that data encrypted today could be at risk in the future, making early migration prudent.
The window for action is open right now, but it won’t stay open forever. The question is whether governments, companies, and individuals will move fast enough to stay ahead of a machine that doesn’t exist yet but is getting closer by the month. Are you ready to bet your data on the answer?