Somewhere between a research lab milestone and a genuine security alert, quantum computing crossed a line that most people weren’t watching. The qubit counts are climbing, government agencies are updating their encryption standards, and security researchers are quietly recalculating timelines they once thought were comfortably far off.
None of this means your password is cracked today. But the gap between “theoretical threat” and “practical concern” is narrowing faster than most headlines suggest, and understanding the mechanics of that shift matters whether you’re an IT administrator or someone who simply banks online.
IBM’s Condor: What Breaking the 1,000-Qubit Barrier Actually Means
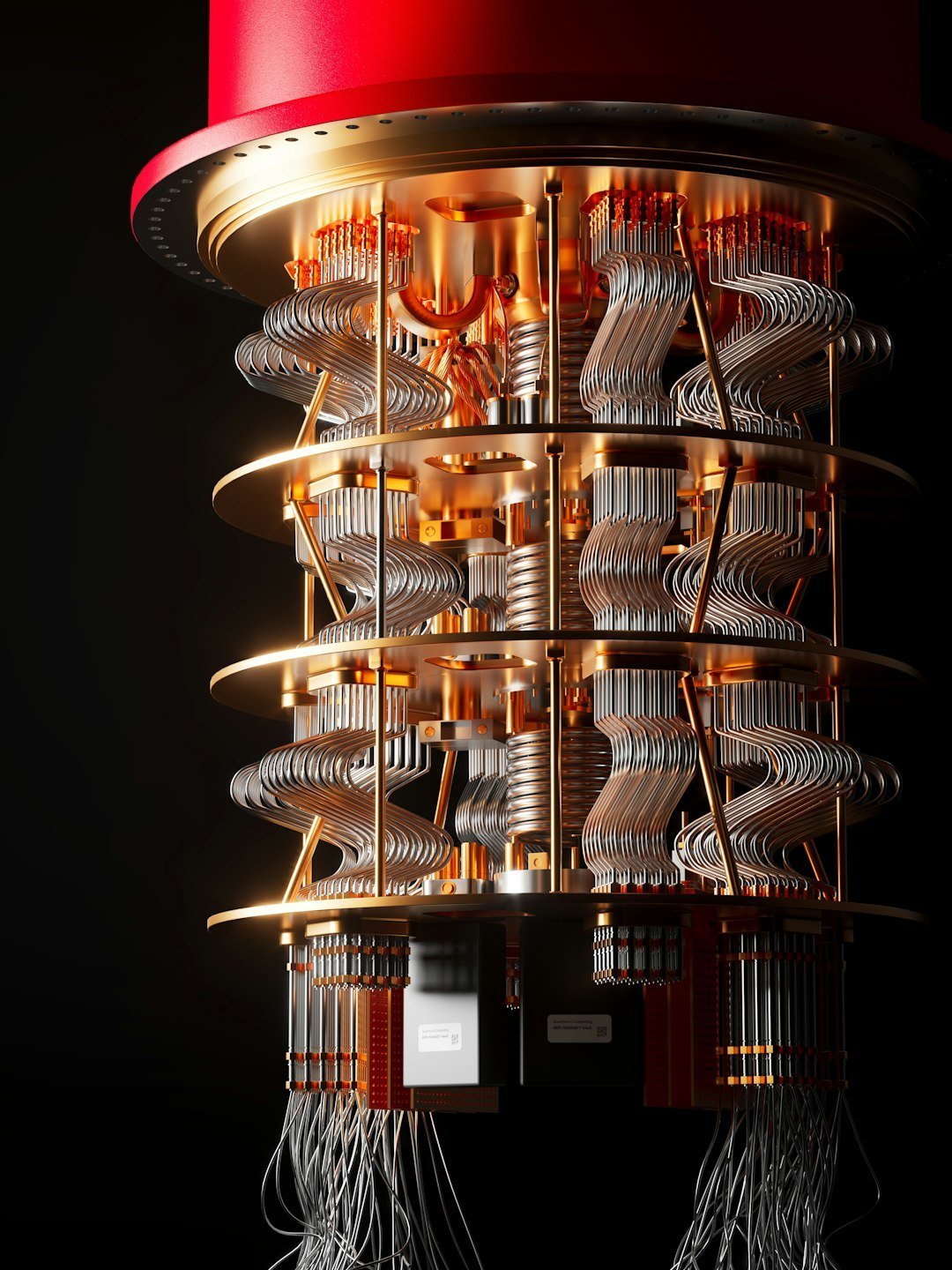
IBM’s Condor is a 1,121-qubit quantum processor unveiled during the IBM Quantum Summit 2023, which took place on December 4, 2023. Condor marks the first quantum chip to surpass 1,000 qubits, a milestone many in the field had eyed as a crucial step toward practical quantum computing.
The processor is built on IBM’s cross-resonance gate technology, and Condor pushes the limits of scale and yield in chip design with a 50% increase in qubit density, advances in qubit fabrication and laminate size, and includes over a mile of high-density cryogenic flex IO wiring within a single dilution refrigerator. Despite its unprecedented scale, Condor’s performance in terms of coherence times and gate fidelity is said to be on par with its 433-qubit predecessor, indicating that IBM managed to grow the processor’s size without a loss in quality.
After revealing Condor, IBM said it would now shift gears and focus on making its machines more error-resistant rather than simply larger. That strategic pivot is significant. Raw qubit count is only part of the picture. Stability and error correction are what will ultimately determine whether a quantum machine can threaten real-world encryption.
How Quantum Computing Threatens the Encryption You Use Every Day

Most online security today relies on a simple mathematical reality: factoring very large numbers into their prime components is extraordinarily time-consuming for a classical computer. Shor’s algorithm allows a quantum computer to factor large integers exponentially faster than any known classical algorithm, making it a direct attack on the security of RSA, DSA, and ECC, which all rely on the difficulty of such problems.
In practical terms, this means that once quantum computers reach sufficient scale and stability, they will be able to crack the public-key cryptographic systems that protect everything from HTTPS connections and digital signatures to secure email and VPNs. Passwords themselves are often protected by different methods, but the keys that secure the channels carrying your credentials are directly exposed.
Traditional asymmetric cryptography is more vulnerable to quantum computing attacks because of Shor’s algorithm. RSA-2048 encryption is the current standard for data sent over the internet, the accepted norm for most applications, and ensures that messages sent online have not been altered. That’s the specific target researchers are racing toward.
The Gap Between Today’s Quantum Machines and Cracking RSA-2048
Breaking a single RSA-2048 key will likely require millions of qubits operating for hours or days, or thousands of qubits operating for months, either way a level of effort utterly beyond the noisy quantum machines of 2025. That’s the honest state of play right now.
The largest quantum processors have just over a thousand physical qubits, and none of them can yet run Shor’s algorithm for anything but tiny demonstration problems. In fact, the largest number ever factored with Shor’s algorithm on real quantum hardware is 21, equal to 3 times 7. The jump from that to a 2048-bit RSA key is not incremental. It’s orders of magnitude.
A May 2025 paper by Google Quantum AI scientist Craig Gidney argues that a fault-tolerant quantum computer with under one million qubits could factor a 2048-bit RSA key in under one week. This represents a stunning 20-fold reduction in qubit count compared to Gidney’s own 2019 estimate, which required roughly 20 million qubits for the same task. Still a formidable machine by any standard, but the trajectory of these estimates is heading in one direction only.
The “Harvest Now, Decrypt Later” Threat Already in Motion

Harvest now, decrypt later is a cybersecurity threat in which encrypted data is collected and stored today so it can be decrypted in the future when quantum computers can break current encryption. The frightening part is that this doesn’t require a working quantum computer today. It only requires patience.
Official advisories from the NSA, CISA, and NIST jointly warn that adversaries may already be harvesting encrypted data with long-term strategic value, intending to decrypt it once large-scale quantum computers emerge. The urgency behind this guidance is underscored by this threat, where any data with a long secrecy lifetime, from critical infrastructure blueprints to personal medical records or state secrets, could be at risk if stolen now and decrypted years from now by a powerful quantum computer.
A breach enabled by quantum computing in 2032 may originate from data intercepted in 2026. By the time the encryption fails, the damage is already done. That reframing is important. The threat isn’t purely future-tense.
NIST’s Post-Quantum Standards: A Real Response to a Real Risk

The U.S. Department of Commerce’s National Institute of Standards and Technology has finalized its principal set of encryption algorithms designed to withstand cyberattacks from a quantum computer. In August 2024, NIST released its principal post-quantum cryptography standards, specifying key establishment and digital signature schemes based on candidates evaluated and selected through a multi-year process.
The standards include three post-quantum cryptographic algorithms: ML-KEM (originally known as CRYSTALS-Kyber), ML-DSA (originally CRYSTALS-Dilithium), and SLH-DSA (initially submitted as SPHINCS+). These post-quantum encryption standards are designed to secure a wide range of electronic information, from confidential email messages to e-commerce transactions that propel the modern economy.
The standards are the result of an eight-year effort managed by NIST, which has a long history of developing encryption. Organizations should begin applying these standards now to migrate their systems to quantum-resistant cryptography. That guidance, notably, isn’t framed as optional.
Quantum-as-a-Service: When the Lab Moves to the Cloud

One underappreciated shift in the quantum landscape is accessibility. These machines are no longer sealed away in government facilities or elite university labs. Major technology firms have opened them up via cloud platforms, making quantum experimentation broadly available for the first time.
IBM has positioned itself as a leader in quantum hardware scaling, with plans to develop a 100,000-qubit quantum-centric supercomputer by 2033. IBM’s June 2025 roadmap update explicitly targets approximately 200 logical qubits by 2029, with IBM announcing it will deliver a fault-tolerant 200-logical-qubit machine codenamed “Quantum Starling” by that year.
Google similarly aims for a useful error-corrected computer by approximately 2029. That’s a short window. The implications for any organization that handles sensitive data beyond a five-year horizon are hard to ignore, especially given the harvest-now-decrypt-later dynamic already described.
How Long Does the World Actually Have?
Forecasts here are genuinely uncertain, and it’s worth being honest about that. Different assumptions about hardware progress, error correction, and engineering bottlenecks produce very different timelines. When asking 46 experts about the prospect of quantum computing being able to crack RSA-2048, researchers found that roughly one third of experts believe it is at least 50% likely to happen before 2031, and more than three in five believe it is at least 50% likely to happen before 2036.
Some believe that cryptographically relevant quantum computers may emerge by 2030, driven by rapid advancements, while many anticipate they could become feasible within 15 to 20 years, requiring significant progress in scaling and error correction. Those windows sound reassuring until you factor in how long it takes large organizations to migrate their cryptographic infrastructure.
The wise approach for cybersecurity professionals is to anticipate the quantum threat well before it materializes, because the lead time to transition global cryptographic infrastructure is on the order of a decade. For most enterprises, that work should already be underway.
What This Means for Ordinary Password Security Right Now

For the average person, the immediate risk remains low. Passwords hashed with modern algorithms like bcrypt or Argon2 are not directly vulnerable to the kinds of quantum attacks described here. The more acute concern sits at the infrastructure layer: the encrypted channels that carry your login credentials, banking sessions, and private messages.
Organizations should begin applying the new NIST standards now to migrate their systems to quantum-resistant cryptography. Cybersecurity products, services, and protocols will need updates, and organizations must identify where vulnerable algorithms are used and plan to replace or update them. That’s the actual to-do list, and it’s long.
Migrating systems to use these new algorithms is going to require a multi-year effort. Organizations are encouraged to begin integrating quantum-resistant algorithms into their systems immediately, as it will take time to transition to the new standards. Early adoption and preparation for quantum computers are crucial to ensure security against future quantum attacks. The window for comfortable preparation is not unlimited.
Conclusion: The Clock Is Running, But So Is the Defense

Quantum computing is genuinely one of the more complex dual-use technologies in modern science. The same capabilities that could accelerate drug discovery and climate modeling also threaten the cryptographic foundations that protect financial systems, government communications, and personal data worldwide.
The reassuring fact is that the defensive response is real, funded, and technically sound. NIST’s new standards exist precisely because the cryptographic community began preparing years in advance. The less reassuring fact is that global adoption of those standards is still incomplete, and the harvest-now-decrypt-later strategy means every day of delay has potential consequences that won’t be visible until much later.
The first consumer quantum processor capable of threatening modern encryption doesn’t exist yet. But the trajectory is clear enough that waiting for it to arrive before responding is no longer a defensible posture. The strongest position is a simple one: treat post-quantum migration as a present-day project, not a future one.