What an Air Gap Actually Is, and What It Isn’t
Air-gapped systems are physically separated from external networks, including the internet, by keeping the computers disconnected from both wired and wireless networks, preventing direct or remote communication with other devices. The idea is simple and intuitive: if there’s no wire, there’s no data path. No data path means no breach.
The most critical military, government, and industrial sites use air gaps to prevent internet-based cyber threats from penetrating the kinds of networks that protect state secrets and human lives. Power grids, nuclear control systems, and classified intelligence networks all rely on this assumption.
The flaw isn’t in the concept. It’s in the assumption that physical isolation eliminates all possible channels. In practice, a computer still generates heat, sound, light, magnetic fields, and vibrations just by running. Every one of those outputs can carry information, whether you want it to or not.
The Fan That Talks: How AiR-ViBeR Works
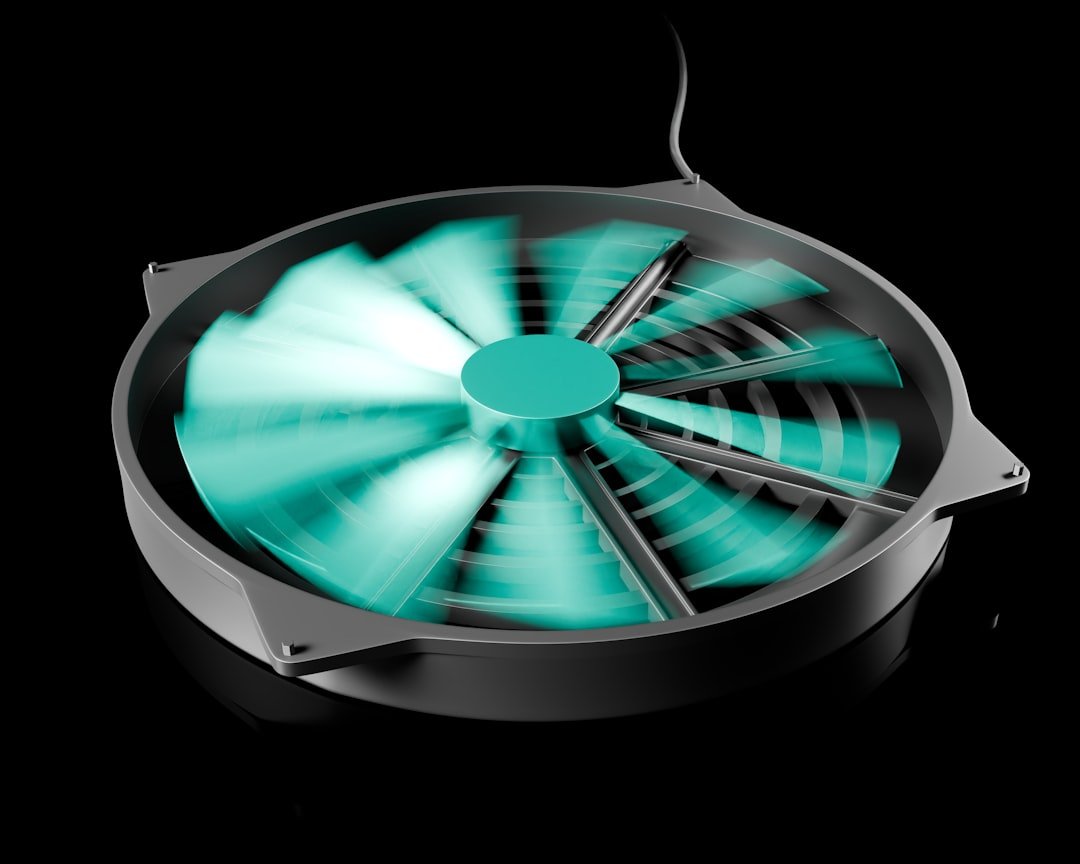
Computers vibrate at a frequency correlated to the rotation speed of their internal fans, and these inaudible vibrations affect the entire structure on which the computer is placed. The attack method is based on malware’s capability of controlling the vibrations generated by a computer by regulating its internal fan speeds.
Malware can regulate the level of mechanical vibrations generated by a computer by controlling its fan rotation speed. These vibrations affect the entire structure on which the computer is placed, and data can be encoded in these vibrations and then received by a smartphone placed on the table via the accelerometer sensor.
A researcher was able to exfiltrate data from air-gapped computers using vibrations produced by controlling the rotation speed of the machines’ internal fans. That researcher was Dr. Mordechai Guri of Ben-Gurion University of the Negev in Israel, whose work on air-gap covert channels has produced one of the most expansive bodies of research in this niche field.
The Smartphone Sitting on Your Desk Is the Receiver

The malware-generated covert vibrations can be sensed by nearby smartphones via the integrated, sensitive accelerometers. Notably, the accelerometer sensors in smartphones can be accessed by any app without requiring user permissions, which makes this attack highly evasive.
To mount such an attack, an adversary would first need to compromise both the air-gapped computer and the mobile phone of an employee. The attack model also assumes that the employee carries the smartphone around the workplace. Once the attacker has compromised the targeted organization’s environment, malware on the transmitter gathers information of interest, then encodes it and sends it to the environment via vibrations on the surface. The nearby infected smartphone receives the data, decodes it, and sends it to the attacker over the internet.
Results show that using AiR-ViBeR, data can be exfiltrated from an air-gapped computer to a nearby smartphone on the same table, or even an adjacent table, via vibrations. That’s a real-world office scenario, not a laboratory abstraction.
Fansmitter: When the Sound Itself Is the Signal

Fansmitter is malware that can acoustically exfiltrate data from air-gapped computers, even when audio hardware and speakers are not present, by utilizing the noise emitted from the CPU and chassis fans. This is a separate but closely related attack vector, using audible sound rather than structural vibration as the medium.
Software can regulate the internal fans’ rotation speed in order to control their acoustic signal, known as blade pass frequency. By modulating that frequency, binary data can be encoded and transmitted without anyone in the room likely noticing anything out of the ordinary.
Using this method, researchers successfully transmitted data from audio-less, air-gapped computers to a mobile phone in the same room, demonstrating an effective transmission at distances of one to eight meters, with a maximum bit rate of 60 bits per minute per fan. The speed is low, but for stealing a password or an encryption key, that’s more than enough.
GPU Fans Are Also in the Picture

The research mainly focused on the chassis fan, which produces the highest level of vibrations, but CPU and GPU fans can also be used. This is significant because modern workstations and servers often carry multiple fans, each a potential independent channel.
GPU-FAN is a documented method for leaking sensitive data from air-gapped machines via covert noise from GPU fans. As GPU hardware has become more prevalent in server environments and machine-learning workstations, the attack surface has grown proportionally.
The data rate in these attacks is deliberately modest. Nobody is streaming video through a fan. But a 256-bit encryption key, a password hash, or a small authentication token can be squeezed through these channels without raising alarm.
The Real-World Precedent: Stuxnet Proved Air Gaps Can Be Crossed

Iran’s nuclear facilities were air-gapped, which means they deliberately weren’t connected to other networks or the internet. It’s thought that Stuxnet was transmitted via USB sticks carried inside these nuclear facilities by agents. That was the first step: get malware onto the isolated system through a physical medium.
Stuxnet was delivered via USB devices and eventually affected around 200,000 computers and 1,000 machines, causing significant physical damage. The air gap held right up until a human walked through it with a flash drive.
The worm also demonstrated that air-gapped networks, long considered a strong defense for critical infrastructure, could be breached through something as simple as a USB drive carried by an unsuspecting employee. Fan-based exfiltration builds on exactly this scenario: malware gets in through a USB or supply chain, then uses physical side channels to get data back out.
A Wider Ecosystem of Covert Channels

Air-gap covert channels are special types of covert communication channels that enable attackers to exfiltrate data from isolated, network-less computers. Various types have been demonstrated over the years, including electromagnetic, magnetic, acoustic, optical, and thermal. Fans are just one instrument in a surprisingly large orchestra.
Previously, researchers demonstrated that it was possible to exfiltrate data from air-gapped systems via heat emissions, HDD LEDs, infrared cameras, magnetic fields, power lines, router LEDs, scanners, screen brightness, USB devices, and noise from hard drives and fans.
Most recently, in September 2024, Guri published the PIXHELL attack. PIXHELL is a new type of covert channel attack allowing hackers to leak information via noise generated by the pixels on the screen, requiring no audio hardware or loudspeakers, where malware generates crafted pixel patterns that produce noise in the frequency range of 0 to 22 kHz.
RAMBO: The 2024 Attack That Leaks Data Through RAM Radiation

The technique has been codenamed RAMBO, short for “Radiation of Air-gapped Memory Bus for Offense,” by Dr. Mordechai Guri, the head of the Offensive Cyber Research Lab at Ben Gurion University of the Negev in Israel. It was published in late 2024 and represents perhaps the most ambitious entry in this research lineage.
Malware on a compromised computer can generate radio signals from memory buses, and using software-generated radio signals, malware can encode sensitive information such as files, images, keylogging, biometric information, and encryption keys. With software-defined radio hardware and a simple off-the-shelf antenna, an attacker can intercept transmitted raw radio signals from a distance.
The RAMBO attack achieves data transfer rates of up to 1,000 bits per second, equating to 128 bytes per second. At this rate, it would take around 2.2 hours to exfiltrate one megabyte of data, so RAMBO is more suitable for stealing small amounts of data like text, keystrokes, and small files. That’s a meaningful constraint, but also a meaningful threat.
How Hard Is This to Pull Off in Practice?

As always with attacks of this kind, it requires the air-gapped network to be first compromised through other means, such as a rogue insider, poisoned USB drives, or a supply chain attack, thereby allowing the malware to trigger the covert data exfiltration channel. The fan-vibration step is not the hard part for a nation-state adversary.
The research team managed to achieve a data exfiltration rate of only half a bit per second through fan vibrations in a test run, suggesting cybercriminals are likely to look to other methods to seize sensitive corporate data. The slow speed and the multi-step infiltration requirement mean this is firmly in the realm of advanced persistent threats and espionage rather than opportunistic crime.
Advanced Persistent Threats in the past have targeted highly secured and air-gapped networks, including USBStealer, Agent.BTZ, Stuxnet, Fanny, MiniFlame, Flame, Gauss, ProjectSauron, and others. The history shows that determined, well-resourced attackers consider air gaps a challenge to overcome, not a hard stop.
What Can Actually Be Done About It?

Countermeasures to block these attacks include enforcing “red-black” zone restrictions for information transfer, using an intrusion detection system, monitoring hypervisor-level memory access, using radio jammers to block wireless communications, and using a Faraday cage.
One of the most effective ways to mitigate the risk is to cover sensitive machines with Faraday shielding, which involves enclosing the computer in a metal case that blocks radio signals from escaping. Other countermeasures include restricting physical access to air-gapped machines, disabling USB ports, and monitoring memory usage for suspicious activity.
The few most sensitive sites on the planet that have to worry about covert channel attacks, including spy agencies, military headquarters, and power plants, have already dedicated significant time and resources to building not just air gaps, but air gaps that make these scenarios impractical. For everyone else, the practical implication is simpler: banning smartphones from secure server rooms isn’t paranoia. It’s now backed by peer-reviewed research.
The Bigger Lesson Behind the Fan
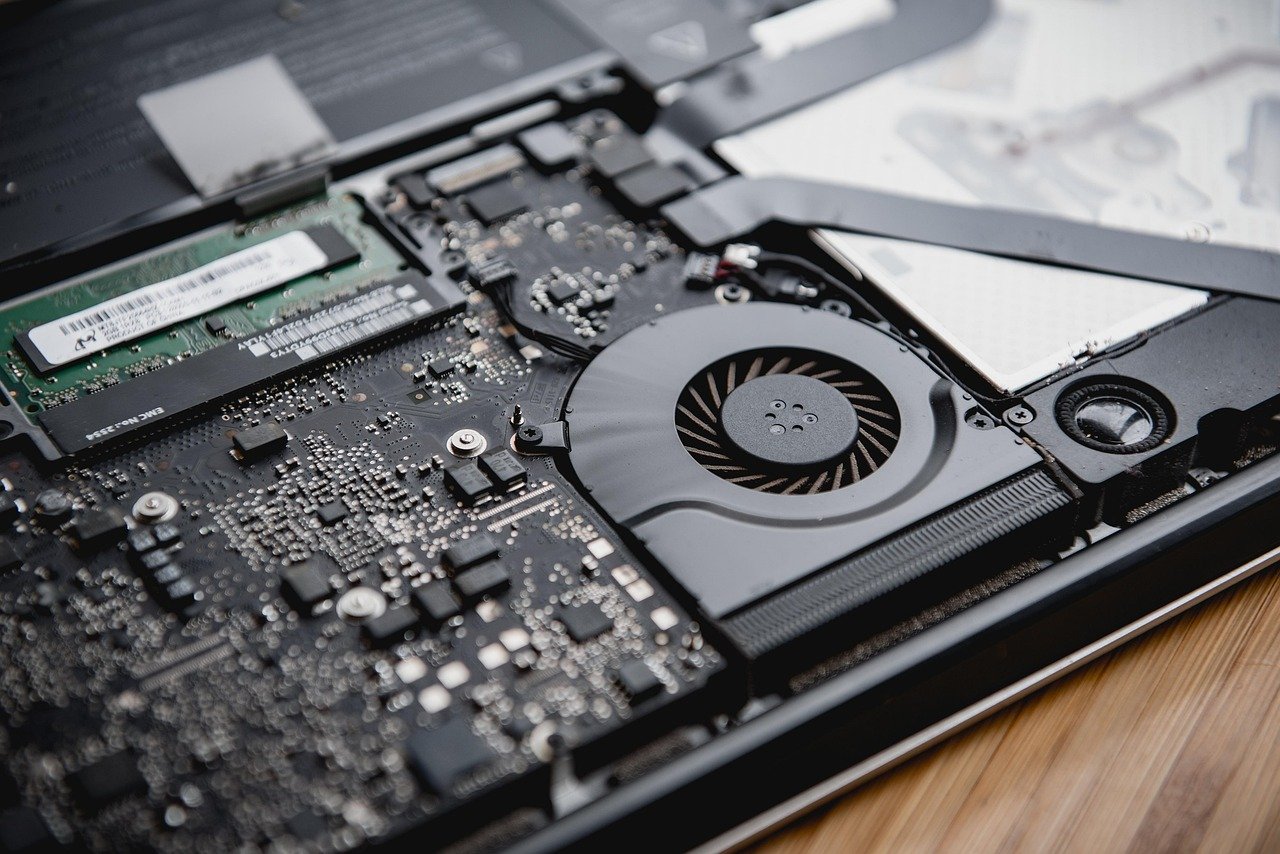
The fan vibration attack is a striking illustration of a deeper principle in security: physical isolation doesn’t mean informational isolation. Any component that can be controlled by software, and that produces any observable physical output, is a potential covert channel. That list covers almost every part of a modern computer.
Despite their perceived reliability and uniqueness, air-gapped systems remain vulnerable to attack vectors that can lead to significant financial loss and physical damage. The research record now spans acoustic, electromagnetic, magnetic, optical, thermal, and vibrational channels, all demonstrated by the same small group of academic researchers working over roughly a decade.
The air gap isn’t dead as a security measure. It still raises the cost of an attack considerably. But it was never the impenetrable wall it was sometimes sold as, and the fan humming quietly inside your secure server is the clearest possible reminder of that.