The Scale of the Problem in 2024 and 2025

The United States alone lost $16.6 billion to social engineering attacks in 2024, a 33% increase from $12.5 billion the previous year. That’s not just a corporate problem. It represents millions of individuals who were talked out of their passwords, credentials, and money by someone they believed was legitimate.
The global average cost of a data breach reached an all-time high of $4.88 million in 2024, and breaches that started with a phishing attack averaged even more – around $4.91 million – according to IBM’s X-Force Cost of a Data Breach Report.
The median time for a user to fall for a phishing email is less than 60 seconds, which means a compromise can happen before any automated security system or analyst has time to react. Speed is part of the weapon.
Phrase #1: “This Is IT Support – We Need to Verify Your Credentials”
A classic pretexting example involves an attacker posing as company IT support staff, contacting employees and claiming they need to verify login credentials for security reasons. By establishing a sense of urgency and authority, the attacker convinces employees to provide their passwords or sensitive data.
Posing as an authoritative figure – such as a government official or senior executive – forces the target into a state of compliance that bypasses normal critical thinking. The word “IT” or “security team” alone triggers deference in most people.
Pretexting, defined as creating a fabricated scenario to extract information, now accounts for more than half of all social engineering incidents and 27% of social engineering breaches, according to the Verizon DBIR 2025. That’s a near-doubling from prior years, and the trend is still climbing.
Phrase #2: “Your Account Will Be Suspended in 24 Hours”
Urgency and scarcity are central tools in the attacker’s playbook. People are more likely to act when pressured into quick decisions or told they’ll miss out on something – hence phishing lures claiming an account will deactivate in 24 hours if the user doesn’t act immediately.
Messages that invoke fear or pressure the target to act quickly are specifically designed to bypass critical thinking. When your brain is in panic mode, it’s not in verification mode. That’s the entire point.
Attackers use emotions like urgency, fear, and curiosity to push people into making unwise decisions such as clicking links, entering passwords, or approving transactions. The phrase works because the emotional response is faster than the rational one.
Phrase #3: “I’m Calling from Your Bank – There’s Been Suspicious Activity”

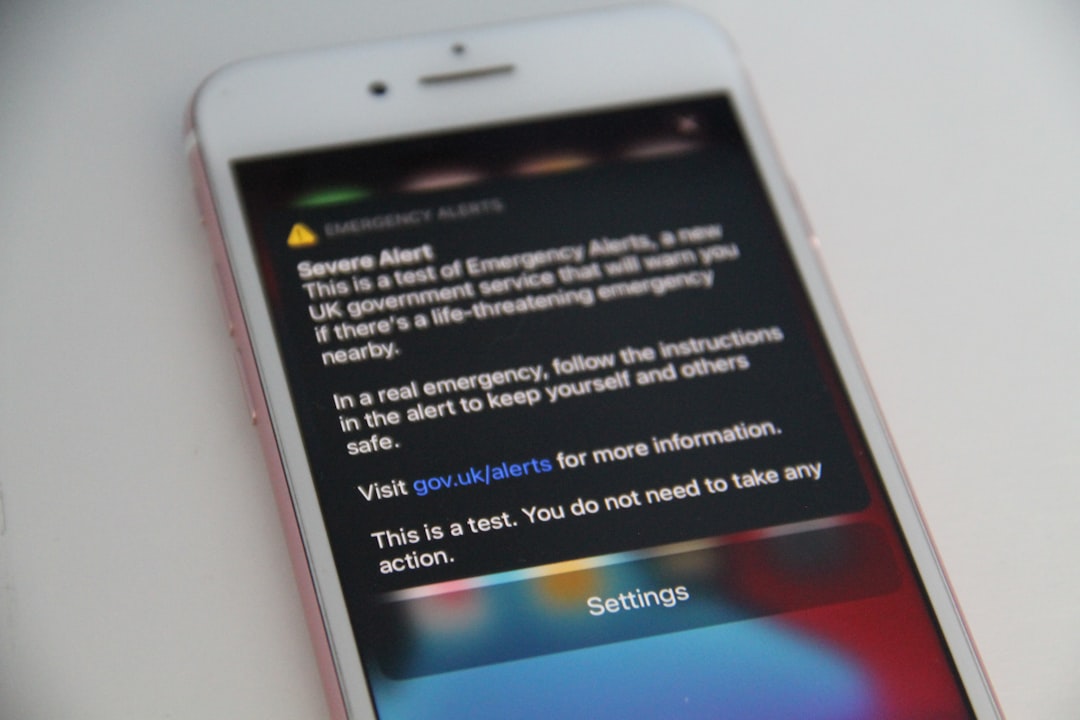
Fraudsters now widely use vishing – a form of phishing that uses voice calls instead of emails. Vishing attacks use social engineering techniques to impersonate legitimate callers, such as bank representatives, tech support agents, or government officials, to trick victims into sharing sensitive information like login credentials or credit card numbers.
Vishing surged 442% in the second half of 2024 alone, making it one of the fastest-growing attack vectors in cybersecurity. The reason is simple: a phone call feels more personal and immediate than an email, and it’s harder to scrutinize in real time.
Phone calls bypass spam filters, email authentication, and most endpoint controls. They exploit trust in the moment, not through a link someone can inspect later. When someone with the right tone and the right script calls you about your bank account, your guard often drops before you even realize it.
Phrase #4: “Are You Available? This Is Urgent and Confidential”

“Are you available?” is a pretext hackers use to determine if their chosen victim is accessible to them and to establish a rapport. It also works to lower the victim’s guard as opposed to immediately making a financial request.
In one documented tactic, the hacker informs the victim that they are planning a special surprise and need their help pulling it off. This serves two ends: it makes the victim believe they’re doing a good deed, and it ensures they won’t inform any colleagues or superiors about the request – which buys the hacker time.
Impersonating high-profile executives is one of the most common tactics used in spear phishing. It puts pressure on the victim to act quickly, and in many cases, this pressure causes a lapse in judgment. The word “confidential” is deliberately added to prevent the target from double-checking with anyone else.
Phrase #5: “We’re Running a Routine Security Check – Just Confirm Your Password”

Attackers craft a believable pretext – posing as a bank representative, government official, or IT support – to establish credibility, then request sensitive details such as passwords, account numbers, or other identifying information.
The attacker uses psychological manipulation to create a pretext – a made-up scenario or identity – to lower the target’s guard. Key psychological tactics include authority, urgency, fear, and trust exploitation. Framing a request as “routine” removes any sense of alarm. It sounds procedural and familiar.
Social engineering remains a preferred access method because it’s easy to execute, infrastructure-light, and often avoids detection. The goal is to leverage trust-based access to bypass hardened controls. No firewall blocks a polite question.
Why AI Is Making These Scripts Far More Convincing
More than 82.6% of all phishing emails analyzed between September 2024 and February 2025 used AI in some form, according to KnowBe4. That means the grammar errors and awkward phrasing that once gave away malicious messages are largely gone.
Threat actors now use generative AI to create personalized emails, deepfake executive voices in phone scams, and simulate real-time chat interactions. In advanced cases, attackers have employed agentic AI – a more autonomous form that can carry out multi-step attacks, such as building fake LinkedIn profiles or creating convincing CVs to land jobs inside targeted firms.
AI can clone a voice from just three seconds of audio, and deepfake-enabled vishing surged 1,633% in Q1 2025 according to Keepnet research. When a caller sounds exactly like your CEO, the script no longer needs to be perfect – it just needs to be plausible.
The Psychology Behind Why These Phrases Work

Authority is one of the most reliable psychological levers in social engineering – people are more likely to follow the orders of perceived leaders, which is why attackers usually impersonate figures such as bank representatives, tech company staff, government officials, or C-suite executives.
Consistency is another powerful lever. People try to remain consistent with their previous statements and actions, so if a victim complies with a request once, they are significantly more likely to comply a second time – even when the new request is larger.
Attackers craft situations that cloud judgment and hinder rational decision-making by understanding how people react under pressure or when faced with tempting opportunities. It’s not about fooling unintelligent people. It’s about catching anyone in a moment of trust.
Who Gets Targeted – and the Real Cost

According to Palo Alto Networks incident response data, attackers used social engineering to breach systems in 36% of investigated incidents, and in two-thirds of those cases, they specifically targeted either privileged or executive accounts.
The average CEO receives 57 targeted phishing attacks every year, according to Barracuda research, making senior leadership among the most persistently targeted groups. Still, the people most likely to be deceived aren’t always in the corner office.
For small businesses, the consequences can be existential – an estimated 60% are forced to shut down within six months of a major cyber breach. For individuals, the loss may be financial, reputational, or both. The phrase that starts it all rarely sounds dangerous when it arrives.
How Pretexting Evolves: New Tricks in 2025

In July 2025, threat actors began testing a new social engineering method called FileFix, which tricks users into pasting disguised PowerShell commands into Windows File Explorer. Unlike earlier attacks, FileFix is subtler, leveraging trusted user behavior without exploiting software vulnerabilities – a sign of how quickly attackers adapt.
In early 2025, social engineering caused roughly 39% of initial access incidents, driven in part by a 1,450% spike in fake CAPTCHA attacks known as ClickFix campaigns. These aren’t clumsy spam blasts. They’re carefully designed to mimic tools and interfaces people use daily.
Nation-state actors have also entered the social engineering space at scale – North Korean operatives, for example, have posed as remote tech workers to gain employment at major corporations, while Iranian-aligned groups such as Agent Serpens have used fabricated institutional identities to distribute malware via spoofed emails and shared document platforms.
How to Stop Falling for the Script

Prevention depends on security awareness training, verification procedures for sensitive requests, and fostering a culture where employees feel empowered to question suspicious interactions – even from apparent authority figures. The word “even” matters there. Most attacks succeed precisely because the source seems authoritative.
Security awareness training reduces phishing click rates by 86% within 12 months, according to KnowBe4 2025 data – suggesting the gap between the problem and the solution is largely a training gap, not a technology gap.
Experts consistently advise enforcing multifactor authentication, vaulting credentials, encrypting communications, and deploying anomaly detection systems that flag irregular patterns invisible to humans. Technology helps, but the real defense starts with recognizing the script for what it is: a rehearsed manipulation, not a routine request.
Every phrase in a social engineer’s toolkit is designed to make a pause feel costly. The most effective protection is simply taking that pause anyway – verifying through a separate channel, slowing down, and treating unexpected urgency as a signal, not a deadline. The attack depends on your cooperation. Withdrawing that cooperation, even briefly, is often enough to end it entirely.